This guide was originally published by Jeremiah Johnson at Tess Pennington’s Ready Nutrition.
Tess is the author of the widely popular Prepper’s Blueprint: A Step-By-Step Guide To Survive Any Disaster

“We are all just prisoners here…of our own device…” – “Hotel California,” by The Eagles
This piece is on the heels of an article released by RT News on 3/8/17, entitled “85% of World’s Smart Phones ‘Weaponized’ by CIA.” The article is a very disturbing report; however, it isn’t something that just “surfaced” out of the zone of unpredictability. The basis for the report stems from the recent WikiLeaks release of the CIA-documents and information that just occurred. Here is an excerpt from that article:
“Google’s Android operating system, used in 85 percent of the world’s smart phones, including Samsung and Sony, was found to have 24 ‘zero days’ – the code name used by the CIA to identify and exploit vulnerabilities for the purpose of secretly collecting data on individuals. The techniques allow the CIA to access data from social messaging platforms, including WhatsApp, Weibo and Clockman before encryption, according to WikiLeaks. Both audio and message data were vulnerable to the exploit through the CIA’s exploitation of gaps in the OS.”
Now mind you, Readers, this piece is not a “news article,” although this event was just reported on 3/8/17. The purpose of this article is to serve as a “wake-up” call, in case you haven’t taken the measures already outlined in previous articles to protect yourself from your own devices tracking, recording, and (essentially) “spying” upon you. You may research past articles on electronic security that you can do, and this piece is a “refresher” that will enable you to secure yourself…. from your own equipment.
4 Ways to Block Your Cell Phone and Prevent Being Monitored
As mentioned in times past, Mylar can be your best ally. Mylar is simple to use, affordable, and it works at blocking the signals going to and from your happy cell-phone tracking and recording device. Here are some inexpensive sources for the Mylar:
- Chip/Snack bags: An infinite variety of sizes are available, and you will have to gauge what size you use after taking the size of your phone/device into account.
- Mylar in the form of “ponchos” or “space blankets”: these are a little more expensive than the chips, but only slightly so. You will end up with more Mylar to use, and the pieces you cut will not need to be cleaned off of salt and other detritus as with the chip bags.
- Freezer bags: Also in a variety of sizes, such as ones that hold up to 30 lbs. of food/ice (for a laptop-sized device) or just a small 1’ x 1’ bag, such as a lunchbag-cooler size.
- Another thing to do is to place your device inside of an ammo can (military issue). In doing so, make sure the rubber gasket around the mouth seals efficiently for a tight seal. There are other containers that can be used; however, you may have to reinforce the seams with something such as Aluminum HVAC duct tape (available for about $15 per roll from your local Home Depot), and cover them over. With the ammo cans, the container is contiguous with only the lid needing that rubber gasket that works.
How to Test for Protection
There is a way to test it out with your phone to see if you have the protection. Take your chip bag or bags. If they’re small, be advised that you will need about three complete layers around the cell phone. Also, place your phone in a plastic Ziploc bag before putting them into the chip bags. This will keep them clean just in case you missed wiping all of the stuff out of them. Wiping out the bags can best be accomplished with a dry paper towel: the oils, salts, and other filth will be caught up by the towel. Just remember to cover/swipe the entire inside surface of the bag.
Then turn your phone on, and turn up the volume of its ring all the way. Next, roll/wrap up your phone and fold it over in at least three complete layers of Mylar. Then use your house phone/landline/etc. to dial your wrapped-up cell phone’s number, and hold the wrapped-up phone close to your ear.
If you did the job correctly, you will not hear a thing. Also, make sure you only ring it 3 times. Any more than that and it may go to a voice-mail/other function, that will send it stored to your cell phone after you unwrap it as a missed call. This way it will not ring it, and the call will have been cancelled.
Remember what General David Petraeus mentioned about the “Internet of things?” Well, those days are upon us. So, what else? You’ll have to figure out the best method for making your layers work and last a long time. You can take the chip bags, cut them open with scissors, and make three premeasured layers. Form a pouch, and cover them inside and out with duct tape. Then you just slip in your phone, and secure the top (fold it over) with whatever type of clamp or clip works for you.
The continuous signal your cell phone sends out (every 4 seconds) will be interrupted. Inconvenient? No. Coordinate with your family members when you will call and talk to them beforehand. Emergency? Pull the phone out of the pouch and use it.
Bottom line: It is a discipline that will have to be followed to enable your privacy…from your own device.
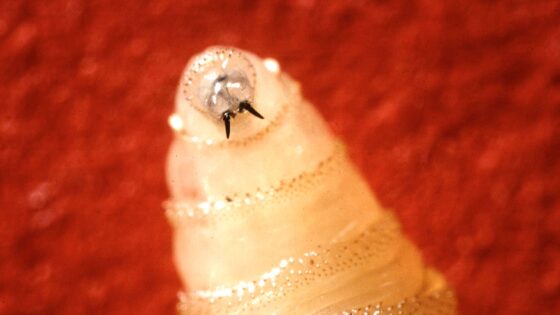
99% of all people carry that thing around with them everywhere. They’re hooked to it more closely than a fetus to the umbilicus: they can’t function without it. But the point I’m making is this: Do you own the phone, or does it own you?
You can accomplish the same thing with your laptops and other “smart” toys…your palm-pilots, blackberries, cameras, and all of the other damnable devices that have made you an unwitting prisoner to the powers and systems that set them in place…not for your “technological convenience,” but for the very purposes of control, dominion, and surveillance over you.
Ammo cans work. The Mylar (when cleaned and fashioned properly) will work. Now you just received confirmation that it is happening, and I’ve given you methods to use to stop it from happening to you. The methods work. I have tested and used them myself. So, without further ado, figure out how much material you need and make one of these pouches for yourself. Your privacy is guaranteed under the 4th Amendment from illegal searches and seizures by the government. That right, however, needs to be exercised by action. So, finish those Doritos, clean out that bag, and wrap that phone up! We’d love to hear of any tips or improvements you have come to trust. Keep fighting that good fight, and send us your comments!
Jeremiah Johnson is the Nom de plume of a retired Green Beret of the United States Army Special Forces (Airborne). Mr. Johnson was a Special Forces Medic, EMT and ACLS-certified, with comprehensive training in wilderness survival, rescue, and patient-extraction. Mr. Johnson is an ardent advocate for preparedness, self-sufficiency, and long-term disaster sustainability for families. He and his wife survived Hurricane Katrina and its aftermath. Cross-trained as a Special Forces Engineer, he is an expert in supply, logistics, transport, and long-term storage of perishable materials, having incorporated many of these techniques plus some unique innovations in his own homestead.
Also See: This is How You Can Dodge Facial Recognition Software
This article first appeared at Tess Pennington’s Ready Nutrition.com.
Tess Pennington is the author of The Prepper’s Blueprint, a comprehensive guide that uses real-life scenarios to help you prepare for any disaster. Because a crisis rarely stops with a triggering event the aftermath can spiral, having the capacity to cripple our normal ways of life. The well-rounded, multi-layered approach outlined in the Blueprint helps you make sense of a wide array of preparedness concepts through easily digestible action items and supply lists.
Tess is also the author of the highly rated Prepper’s Cookbook, which helps you to create a plan for stocking, organizing and maintaining a proper emergency food supply and includes over 300 recipes for nutritious, delicious, life-saving meals.
Visit her web site at ReadyNutrition.com for an extensive compilation of free information on preparedness, homesteading, and healthy living.







0 Comments